Trump-Kim Summit Draws Hackers’ Attention
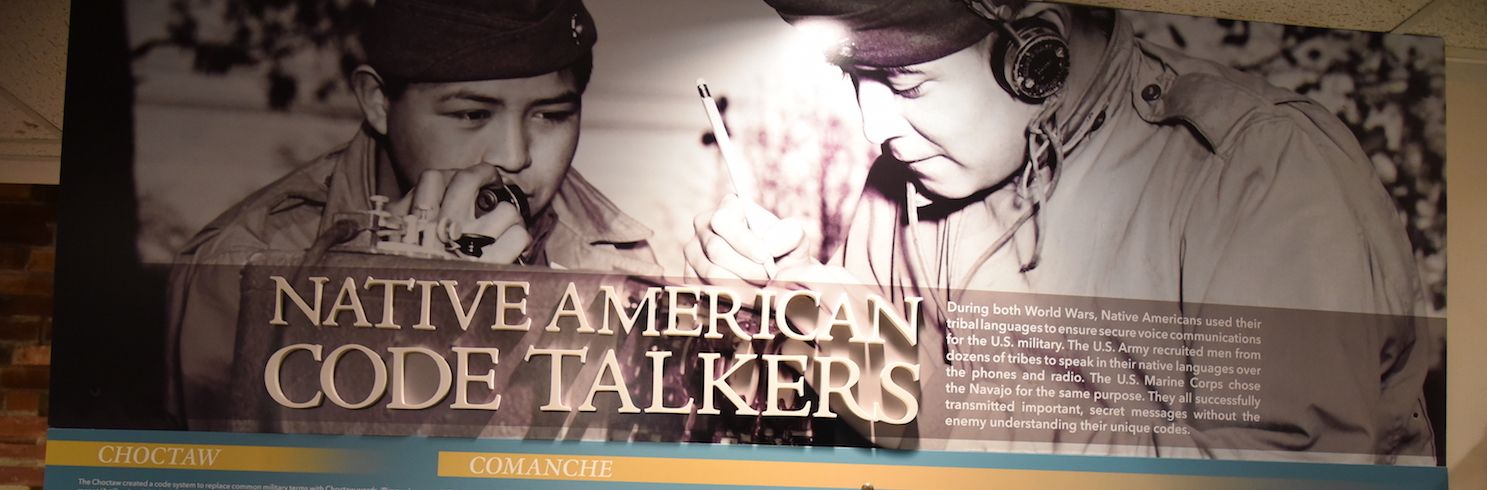
Cyberattacks, mostly from Russia, targeted Singapore on 11-12 June during the summit between U.S. President Trump and North Korean leader Kim Jong Un. A total of 40,000 cyber attacks were directed against Singapore from 11:00 pm on 11 June until 8:00 pm on 12 June. Cyber researchers state that 88% of these attacks came from Russia, and 97% of Russian-based cyber attacks were targeted at Singapore during the same period. Brazil was the second-highest source of attacks. Most of the attacks were focused on VOIP phones port SIP 5060, used for plain-text messaging. The Telnet port was the second most-targeted in the attacks. This port is typically associated with attacks on Internet of Things devices, suggesting that the attackers were looking for devices to target for intelligence collection. Researchers stated that they couldn’t attribute the Russian-based attacks to government organizations, although it is common knowledge that the Russian government hires proxy groups to conduct cyber operations on its behalf. SecurityWeek.com
Android Mystery Bot Has Many Capabilities
Researchers at Threat Fabric discovered a new type of Android malware that contains a banking trojan, keylogger, and ransomware simultaneously delivered in a single package. Researchers at first thought the malware was a form of Lokibot, but upon further review determined that the new malware had significant differences, although the two types of malware may have been developed by the same threat actor. Mystery Bot can target Android versions 7 and 8 in addition to older Android versions. Researchers noted several other features present in the malware but not yet deployed, suggesting that Mystery Bot is still in the developmental stage. ZDnet.com
ClipboardWalletHijacker Malware
Qihoo 360 researchers discovered a new malware designed for stealing cryptocurrency. As indicated in the name, this malware lurks on the clipboard of unsuspecting users to identify any cryptocurrencies in the user’s online wallet. If it finds an address associated with a cryptocurrency like Bitcoin or Ethereum, the malware replaces the address with one used by the cybercriminals who then steal the money. ClipboardHijackerWallet has similar functionality to previous cryptocurrency-focused malware such as ComboJack and CryptoShuffler. Researchers recommend that people using their computers to trade cryptocurrencies use hardware-based wallets instead of online wallets that are vulnerable to these attacks. Hackread.com
Follow the Money – If You Can
A Connecticut law firm received an email from an attorney in North Carolina asking for help in collecting funds for a client in China from a Connecticut company. The “client” then contacted the law firm and formalized an agreement to collect the funds and transfer them to the “client.” The law firm then received a check from a North Carolina bank for $200,000, deposited it, and issued a check to the “client’s” account in South Korea. The only problem was that the North Carolina check was phony and neither the North Carolina lawyer, the Connecticut firm, nor the actual client company were aware of the transaction. The entire scenario was concocted and executed by a cyber scammer, who is now $200,000 richer. ABA Journal
More Intel Vulnerabilities Revealed
A second round of Intel vulnerabilities allows attackers to access sensitive information, including encryption keys, according to a report of 14 June. LazyFP (CVE 2018-3665) is one of a secondary set of processor vulnerabilities that follows the earlier notification about Spectre and Meltdown. LazyFP was discovered by researchers at Amazon and Cyberus Technology early in 2018. Intel has delayed release of a white paper explaining the vulnerability. Speculation is that the flaw is in the use of the Floating Point Unit and associated registers in the processor. Apple Insider, 14 June 2018
Return to our HOME PAGE.