-
 EDUCATE
EDUCATE...our citizens to be cyber smart, and develop pathways for the future cyber workforce.
-
 ENGAGE
ENGAGE...and convene partners to address emerging cyber and cryptologic issues.
-
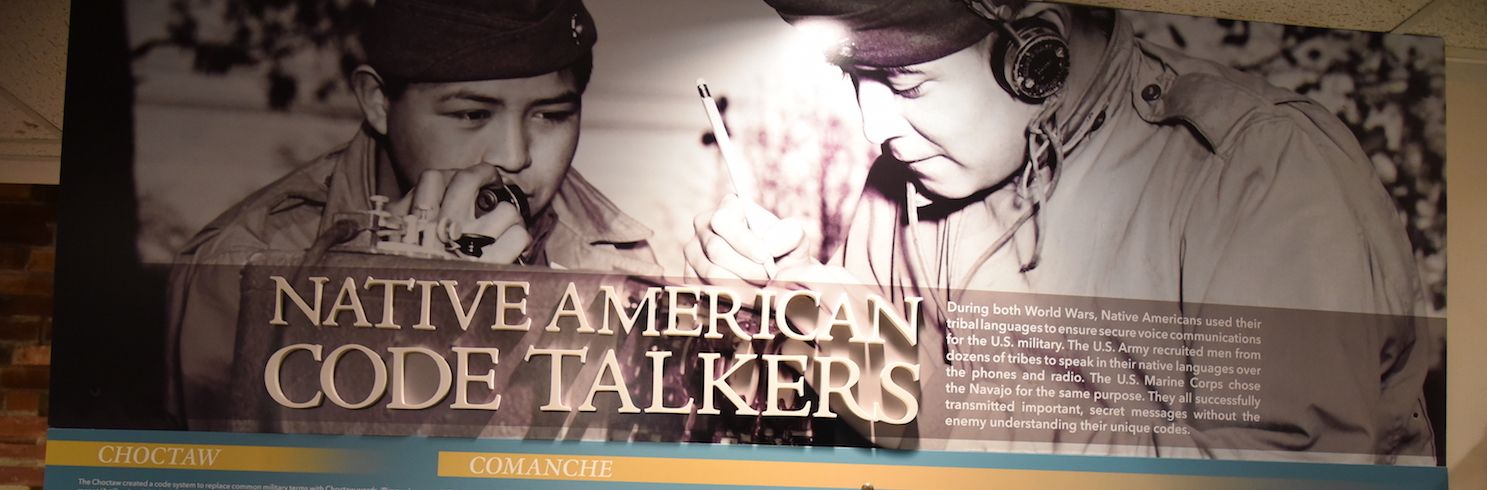
 COMMEMORATE
COMMEMORATE...our cryptologic history & those who served within the cryptologic community.
The National Cryptologic Foundation is a private 501(c)(3) organization not affiliated with the U.S. Federal Government.
Return To List
Cryptologic & Cyber Dates in History
-
15 May 1942: President Roosevelt signs bill into law, creating the Women's Army Auxiliary Corps (WAAC), the women's branch of the United States Army. In July 1943, it became the Women's Army Corps (WAC).