Your content goes here. Edit or remove this text inline or in the module Content settings. You can also style every aspect of this content in the module Design settings and even apply custom CSS to this text in the module Advanced settings.
Your content goes here. Edit or remove this text inline or in the module Content settings. You can also style every aspect of this content in the module Design settings and even apply custom CSS to this text in the module Advanced settings.
Your content goes here. Edit or remove this text inline or in the module Content settings. You can also style every aspect of this content in the module Design settings and even apply custom CSS to this text in the module Advanced settings.
Your content goes here. Edit or remove this text inline or in the module Content settings. You can also style every aspect of this content in the module Design settings and even apply custom CSS to this text in the module Advanced settings.
Your content goes here. Edit or remove this text inline or in the module Content settings. You can also style every aspect of this content in the module Design settings and even apply custom CSS to this text in the module Advanced settings.

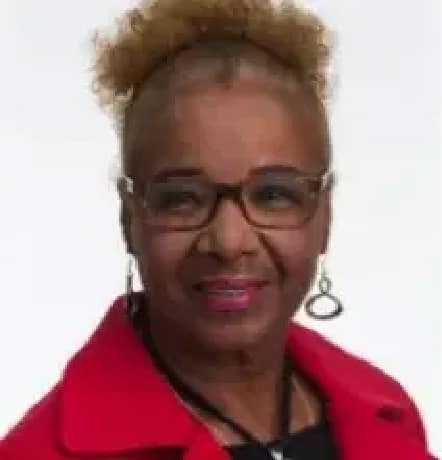
Lillie Berry
Ms. Lillie Berry began her career at Arlington Hall in 1956 as a clerk typist in the signals analysis unit. She quickly learned the terminology and pressed analysts to explain to her the concepts. After attending a signals analysis course and mastering a basic understanding of the subject, she was requested, in the early 1960s, to teach portions of the introductory material. She, thus, became the first African American woman in the Agency to give instruction in that discipline. In 1968, she marked another first when she became the first ...

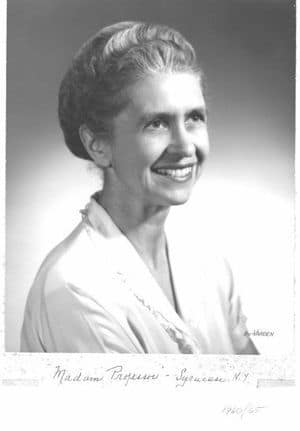
Dr. Sarah “Sally” Botsai
Sarah “Sally” Botsai started work at NSA in 1957 shortly after her college graduation. She continued her education eventually earning her Ph.D. in International Relations in 1972.
Dr. Botsai spent twelve years in Operations before she was selected as the first woman to serve as the NSA representative in the White House Situation Room. After her two-year tour in this position, she was asked to return as the Deputy Director of the White House Situation Room. She held this position until 1976. She was also the first NSA woman to attend the National War College from which she ...

Eileen Buckholtz
Eileen Buckholtz was one of the first people hired as a computer scientist by the National Security Agency. Known as one of the Agency’s Queens of Code – she helped bring graphical user interface systems (early word processors) to life. Eileen passed her passion along to new generations of computer scientists, working on the programming behind the first eReader. She is now penning STEM-themed children’s books.

Ann Caracristi
Ann Caracristi came to work as a cryptanalyst with the Army Signal Intelligence Service in 1942. She helped pioneer the application of early computers in cryptanalysis and established a laboratory for studying new communications phenomena.
Her expertise and professionalism responding to tough intelligence problems brought her rapid advancement at NSA. In 1959, she was promoted to supergrade, and in 1975, she became the first woman at NSA to be promoted to GS-18. She was the first woman to be named NSA Deputy Director in 1980. Also in 1980, she ...
Wilma Davis
With a degree in mathematics and a Navy correspondence course on cryptology, Wilma Davis was hired to work in the Army's Signal Intelligence Service in the late 1930s. Her first assignment was with the Italian diplomatic codes, which she exploited until 1942 when she transferred to the Japanese problem. Within two years, she was the head of the department that solved and processed intercepted Japanese Army code messages. At the end of the war, she moved on to the Chinese team and then to the Venona Project trying to break Soviet messages.
Ms. Davis left the cryptologic field a ...
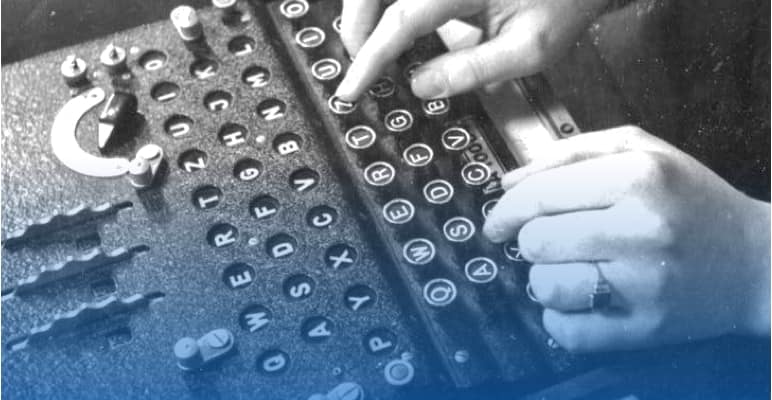
Agnes Meyer Driscoll
Agnes Meyer Driscoll held degrees in mathematics and physics, as well as proficiencies in English, French, German, Latin, and Japanese. She was a pioneer cryptologist and a Navy code breaker. One Navy admiral described her as "without peer as a cryptanalyst." From solving codes and breaking Japanese naval systems, to developing new cipher machines and encouraging the use of tabulating machines for cryptanaysis, her accomplishments are inspirational.
Ms. Driscoll's work as a navy cryptanalyst who broke a multitude of Japanese naval systems, as well as a ...
The Forgotten Female Programmers Who Created Modern Tech
Article excerpt below....
If your image of a computer programmer is a young man, there's a good reason: It's true. Recently, many big tech companies revealed how few of their female employees worked in programming and technical jobs. Google had some of the highest rates: 17 percent of its technical staff is female.
It wasn't always this way. Decades ago, it was women who pioneered computer programming — but too often, that's a part of history that even the smartest people don't know.
I took a trip to ground zero for today's computer revolution, Stanford ...

Elizebeth Smith Friedman
Elizebeth Smith Friedman is often referred to as the wife of cryptologist William Friedman. However, this female pioneer in code breaking was actually the one to introduce him to the field. In January 2021, PBS aired a special documentary about Elizebeth Smith Friedman, based upon the book "The Woman Who Smashed Codes" by Jason Fagone. Click on the links below to learn more.
Elizebeth Friedman was a wife, mother, writer, Shakespeare enthusiast, cryptanalyst, and pioneer in U.S. cryptology. She enjoyed many successes in cryptology in her own right and has been ...

Lee Ellen Hanna
An alumna of the National War College, Lee became the first woman senior operations officer in the National SIGINT Operations Center before being promoted to the NSA’s senior executive level, including serving as deputy director of human resources and leading some of the Agency’s most mission-critical organizations.
As part of her responsibilities, Lee briefed presidents and addressed Congress, led several intelligence production organizations, chaired an NSA oversight panel on processes and management of the Agency’s personnel office, and worked closely with U.S. intelligence ...
The Hello Girls – by Elizabeth Cobbs (A Review)
2017 NPR Book Review by Glen Weldon of "The Hello Girls" by Elizabeth Cobb
During World War I, some 223 members of the U.S. Army Signal Corps performed a highly specialized service which demanded great skill, nerve and tenacity: Over the vast network of telephone lines that had been hastily constructed across France, these soldiers worked the complicated switchboards connecting the ever-shifting front lines with ...
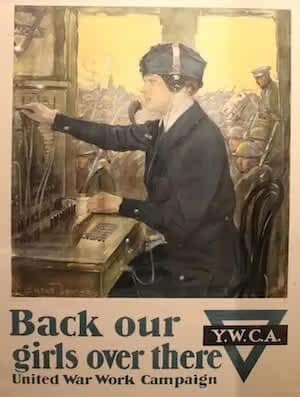
Hello Girls
We salute the “Hello Girls.”
Communication, in this case telephone lines, were crucial to planning and coordinating military campaigns. In World War I, men of Army’s Signal Corps constructed telephone lines along the front, but proved lacking as operators. Professional telephone operators were needed to connect the calls between major entities of the Allied effort, working even on the “fighting lines.”
The Army turned to the professional women operators in the United States. Not only were these women expected to be experienced telephone operators, they also needed to ...

Genevieve Young Hitt
Genevieve Young Hitt (1885-1963) - As a young Texas debutante, Ms. Hitt probably never suspected she would one day be described as "the U.S. Government's first female cryptologist."
She likely developed an interest in cryptology alongside her husband, Colonel Parker Hitt. Ms. Hitt demonstrated a clear knack for cipher work and aside from a brief visit to Riverbank Laboratories, was self-taught. She initially deciphered messages without salary and in 1918 became a salaried Army employee, performing code work for $1,000 per year. She has also been credited with ...
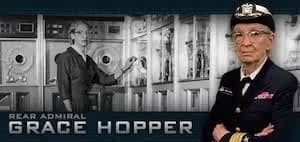
Grace Murray Hopper
At the age of seven, she was already taking apart alarm clocks, determined to figure out how they worked. Often deemed “The Queen of Code,” Grace Hopper was an American computer scientist and United States Navy rear admiral.
A pioneer in the field, she was one of the first programmers of the Harvard Mark I computer in 1944, and invented the first compiler for a computer programming language. She popularized the idea of machine-independent programming languages, which led to the development of COBOL, one of the first high-level programming languages. She is credited with ...

Minnie McNeal Kenny
Minnie McNeal Kenny served as a civilian for 43 years. She joined NSA as a communications clerk at the GS-4 level, higher than the starting grades offered to African Americans at the time. She was an expert in the fields of language, cryptanalysis, and traffic analysis. Throughout her tenure, she worked to further the cause of minorities at NSA. Her legacy was not only in the impressive changes she effected in NSA structure, policy, and practice, but in the inspiration she was to all NSA employees, regardless of race, giving them faith that they could effect ...

Hedy Lamarr
Well known for her role as a movie star and a beauty icon, Hedy Lamarr is less well known for her invention of spread spectrum technology. By manipulating radio frequencies at irregular intervals between transmission and reception, the invention formed an unbreakable code to prevent classified messages from being intercepted by enemy personnel. Needless to say, this achieved great things for U.S. military ships, but it also served as a basis for modern spread-spectrum communication technology, such as Bluetooth, COFDM (used in Wi-Fi network connections), and CDMA (used in some ...

Google Doodle Honors Hedy Lamarr
November 9th 2015 would have been Hedy Lamarr's 101st birthday!
Google decided to honor her with one of their famous Google Doodles, created by "doodler" Jennifer Hom. And of course this one is animated. A mini-movie - appropriate for a famous actress!
Below is the write-up about the Doodle. Please also visit the Google Doodle page to see the Doodle since it is animated. The included image is just one image from the mini-movie. You can also see images of the artist's ...

How Hedy Lamarr Invented Early Wireless Technology (Article Excerpt)
Excerpt from IQ Intel
How Hedy Lamarr Invented Early Wireless Technology
by Karli Petrovic, iQ Contributor and Writer (no longer available online)
Unhappy being pigeonholed due to her looks, the “most beautiful woman in the world” set out to develop a secret communication system that would take down Nazi submarines.
A lonely immigrant from Austria slips out of her stage clothes and kicks off her heels. Carefully removing her movie makeup, she’s dissatisfied that she’s been overlooked for more significant roles. Instead of throwing a pity ...

Ada Lovelace
Ada Lovelace (Augusta Ada Byron, Countess of Lovelace) – (1815-1852) The daughter of famed poet Lord Byron, Ada Lovelace was a gifted mathematician and is credited with having written instructions for the first computer program. While translating an article for Charles Babbage about Babbage’s engine, she added her own notes and ideas which ended up being much longer than the original article. In her article, she described how codes could be developed to handle letters and symbols, as well as numbers. She also theorized a method for the device to repeat a series of ...

Barbara McNamara
Barbara McNamara demonstrated extraordinary leadership qualities in advancing NSA’s mission, enhancing cooperation with other US agencies, and developing foreign partner relations. She began her career as a Chinese Linguist and served in several analytic, operational, and managerial positions at the National Security Agency (NSA).
In 1994, she became the first woman to be Deputy Director of Operations, and in 1997, she reached the highest civilian position at NSA when she was named the Agency’s Deputy Director. In 2000, she became the first woman to hold the ...

Juanita Moody
In early 1943, Juanita Morris, at a small college in North Carolina, wished to contribute to the war effort and volunteered at the nearest recruiting office. By April, she was at the Army cryptologic headquarters at Arlington Hall Station. While awaiting her security clearance, the Signal Security Agency (SSA) put her into unclassified training in cryptanalysis; she became fascinated with the subject.
At the end of the war, her supervisor asked her to stay on, rather than be demobilized, and she agreed. In 1948, she married Warren Moody, a non-cryptologic ...
Dr. Loyce Pailen
Dr. Loyce Pailen, a doctor of management and senior director of the Center for Security Studies at University of Maryland Global Campus (UMGC), has more than 35 years of experience in information technology, including work in cybersecurity, software development, project management, telecommunications, risk management, and network and systems security and administration. She has held director-level information technology positions at the Washington Post, Graham Holdings, UMGC, and as a contractor at Computer Sciences Corporation for the Defense Cyber Investigations Training Academy ...

Debora Plunkett
Debora Plunkett is a leader with more than 30 years of experience leading large, complex organizations. Culminating a career of U.S. federal service in 2016, she currently is Principal of Plunkett Associates LLC, a consulting business. She is a Senior Fellow at Harvard’s Belfer Center for Science and Technology and an Adjunct Professor of Cybersecurity in the University of Maryland’s Graduate School. She serves on the corporate boards of JCPenney, CACI International, and Nationwide Insurance. She is also a founding member and Chairman of the Board of Defending Digital ...

Dr. Julia Ward
As the founder of Central Reference, Dr. Julia Ward significantly affected the future of a key function across a wide variety of targets and problems. Her pioneering efforts to build a library of classified and unclassified resources to aid analysis greatly advanced the American cryptologic effort.
Dr. Ward was born in December 1900. She attended Bryn Mawr College, earning an Associate Bachelor's degree in 1923 and a Ph.D. in 1940. She was employed by Bryn Mawr from 1923 until she joined the cryptologic service during World War II. She held a variety of positions of increasing ...

Wilhelmena Ware
Ms. Wilhelmena Ware began her career at the Agency in 1949 as a cardpunch operator. In 1952, she was promoted to a supervisory position and in that capacity taught a comprehensive keypunch course to the Agency’s first hearing impaired employees. Later, Ms. Ware became a computer science instructor in the National Cryptologic School and taught Introduction to Computer Systems Operations. Ms. Ware was promoted to Chief of the Learning Center where she was instrumental in instituting a number of programs, including the implementation of the sign language course. In 1980, ...

US Navy Waves
On 30 July 1942, the WAVES were established. The name was an acronym for "Women Accepted for Volunteer Emergency Service" (as well as an allusion to ocean waves). Their official name became the U.S. Naval Reserve (Women's Reserve), but the nickname "WAVES" stuck. The word "emergency" in WAVES implied that the acceptance of women was due to the unusual circumstances of World War II, and at the end of the war the women would not be allowed to continue in Navy careers, but it or its successors continued for decades afterwards. On 12 June 1948, women gained permanent status in the armed ...

Dr. Nancy K. Welker
Dr. Nancy K. Welker is a physicist and nationally recognized expert in superconducting electronics. She was a pioneer in technology development in Maryland and nationwide. During her 55-year distinguished career with the National Security Agency (NSA), she led groundbreaking research in superconducting materials and integrated circuit manufacturing, which made it possible to develop a new generation of faster and more powerful computers. Dr. Welker earned an A.B. in physics in 1963 from Mount Holyoke College, and her M.S. and Ph.D. in physics from American University. ...
Eunice Russell Willson Rice
Eunice Russell Willson Rice was a pioneering US Navy cryptologist who successfully broke Italian and Japanese codes during WWII. She joined the Office of Naval Intelligence as a language analyst in 1935 and transferred to OP-20-G—the Office of Naval Communication’s Code and Cipher Section—as a civilian cryptanalyst in 1939. During WWII, Rice led the team working Italian ciphers and codes, then learned enough Japanese on her own to lead the team charged with recovery and analysis of the vital Japanese Water Transport code.
Degrading the Japanese Merchant Marine ...