“Any Man-Made Code Can Be Broken by a Woman”
The groundbreaking female naval cryptographer who helped change the course of World War II.
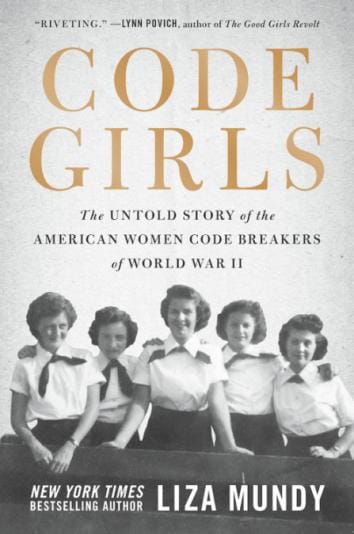
By Liza Mundy
Click Here to view the full article on Slate.com.
This essay is adapted from Code Girls, by Liza Mundy, published by Hachette Books.
Many people cheered earlier this year when Yale University decided to strip the name of slavery advocate John C. Calhoun off one of its residential colleges and rename that piece of elite real estate Hopper College, after naval Rear Adm. Grace Murray Hopper. The storied computer pioneer also has a conference named after her, the Grace Hopper Celebration, which has grown into one of the biggest annual gatherings for women in computing and tech. Now that Hopper is finally getting her due—as are the black American mathematicians of Hidden Figures—other schools may look for important hidden female figures whose names deserve to be chiseled into dorms or academic buildings.
If so, they would do well to consider another early Navy woman and cybersecurity pioneer, the brilliant Agnes Meyer Driscoll. Her groundbreaking cryptanalytic work during and before World War II saved countless lives and immeasurably advanced the field of cryptanalysis, or codebreaking, and with it the science of encryption and cybersecurity. It is no exaggeration to say that she was a key, unsung reason why the U.S. won the Battle of Midway—one of the most famous sea battles of all time—and eventually, the Pacific War.
Agnes Meyer was a brilliant young teacher who would become one of the great cryptanalysts of all time. Born in 1889 in Illinois, Meyer studied mathematics, music, physics, and foreign languages. She was heading up the math department at Amarillo High School in Texas, when the United States declared war on Germany in 1917. She enlisted at age 28, one of the first women to do so, starting out as a stenographer but soon was assigned to the Navy’s postal and censorship office. The Navy transferred her to its code and signal section at a time when the unit’s purpose was protecting naval communications—encoding America’s own messages. Agnes Meyer got her start making codes, which is the best possible training for learning how to break them.
Get Future Tense in your inbox.
After the Great War ended, Agnes Meyer was discharged along with the other reservists. Her abilities were such that the Navy promptly hired her back as a civilian. As part of her duties, she was given the task of testing what were known as “nut jobs”: machines marketed by inventors offering foolproof enciphering systems.
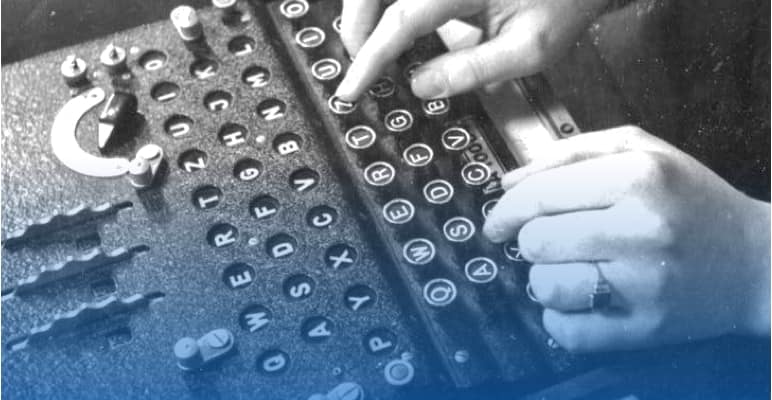
Technically, there are two kinds of secret message systems. One kind is a code, in which an entire word or phrase is replaced by another word, a series of letters, or a string of numbers, known as a “code group.” If secrecy is your goal, the best code is one in which code groups are randomly assigned. Codes are compiled and kept in codebooks, not unlike dictionaries, where the encoder can look up the word or phrase and the corresponding group that stands for it. But even random codes have an obvious vulnerability: Repetitious use of the same code groups in messages enables codebreakers to tease out their meaning from context or position.
The other type of system is called a cipher, in which a single letter or number is replaced by another single letter or number. Ciphers can be created by scrambling letters, or by replacing individual units with other units, a method called substitution. For centuries, ciphers were created by hand. But when radio and telegraph came along, messages could be sent much faster. Machines were needed that could encipher rapidly. Because the sheer volume of messages meant it was easier to spot simple patterns, more complicated ciphers were needed, too. These machines created an early form of what would later be called encryption.
Agnes Meyer hacked the nut jobs—she broke enemy devices and examined machines that inventors were peddling to the U.S. Navy, uncovering their flaws and weaknesses. After a brief stint in the private sector, she returned to the Navy as a civilian. “She not only trained most of the leading naval cryptanalysts of World War II,” wrote one intelligence officer, Edwin Layton, “but they were all agreed that none exceeded her gifted accomplishments.” Though she did not get any public credit, she laid much of the groundwork that made their exploits possible.
By the 1920s the American Navy, sensing in Japan a future naval adversary, was beginning to harbor code-breaking ambitions. And so U.S. Navy ships began intercepting Japanese messages and building more Pacific intercept stations. In New York City, in 1923, naval intelligence officers surreptitiously raided the office of the Japanese consul general, where they rifled a steamer trunk, found a 1918 naval codebook, stole it, photographed each page, put the book back, and sent the pages to Washington. All of which ended up in the competent hands of Agnes Meyer, who became Agnes Meyer Driscoll when she married an attorney.
Neither Driscoll nor anybody in the Navy operation had seen an additive cipher, but she figured it out.
By then, a “research desk” had been set up at Navy headquarters. The desk was staffed by a small number of people, civilians as well as some reluctant naval officers. Cryptanalysis is shore duty, an office job. In the U.S. Navy, if you were a career naval officer with any ambition, shore duty was not what you wanted. And so officers came and went from the research desk, studying for a couple of years and then shipping out to sea.
Driscoll sat perpetually at the research desk, a civilian and a woman and therefore sentenced to permanent shore duty, unlocking the secrets of Japan’s naval fleet code. A fleet code is the main system that bases, ships, and organizations use to talk with one another about strategy and tactics, logistics, intelligence, morale, ship movements, situation reports, even weather. Agnes Driscoll studied the stolen codebook day after day, year after year. She liked to say that “any man-made code could be broken by a woman.”
She figured out how the Japanese disguised their fleet code using a method called “superencipherment” that involves both a code and a cipher. For the main fleet code, the Japanese were using a large codebook containing thousands of three-character code groups that stood for Japanese words, syllables, phrases, and even punctuation marks. Once a clerk wrote out a coded message, he then enciphered each character, so that the code group would be sent as a different set of characters entirely. The “research desk” knew what the code groups stood for, thanks to the theft of the codebook, but that didn’t do them any good. When they intercepted an actual message, the groups they were looking at had been enciphered. They had to figure out how to get rid of the encipherment and restore each code group to its original form.
The tiny Navy team worked for years to achieve this. The breakthrough came when Driscoll discerned that the encipherment was accomplished by transposing or switching the position of the characters.
Successful code-breaking often comes down to diagnostics: the ability to see the whole rather than just the parts, to discern the underlying system the enemy has devised to disguise its communications. The Japanese, Agnes diagnosed, were encoding their messages and then using something called columnar transposition, which involves writing the code groups out horizontally but transmitting them vertically, aided by a grid with certain spaces blacked out, whose design changed often. The intelligence gleaned provided insight into Japanese fuel supplies, ship accidents, aviation advances, naval maneuvers, and strategy for conducting combat operations against the United States. It also revealed that the Japanese were alarmingly well-versed in America’s own naval war plan.
Mastering the fleet code was a never-ending undertaking, for the Japanese and for Agnes Meyer Driscoll. As a security measure, the Japanese Navy periodically changed its codebooks-burning the old codebooks, printing new books, and distributing them to every ship, office, and island. When this happened, each word would be assigned a new code group, and the American codebreakers would have to start from scratch. Sometimes, the changes were even bigger: In 1931, Thomas Dyer, then a trainee, was puzzling over a new intercept; Driscoll walked up behind him, took his worksheet, looked at it, and said, “The reason you’re not getting anywhere is because this is a new code.”
She was right. The Japanese had changed their system, coming up with code groups that were longer and organized in a tougher, more complex way. Puzzling out the new system took three years, and once again it was Driscoll who did the bulk of the work in cracking one of the most complicated systems ever seen. In 1936, her efforts revealed that the Japanese had refitted a battleship that now could travel in excess of 26 knots. The United States didn’t have a ship that fast, so the Navy upgraded a new class of battleships to exceed that speed.
Then the code system changed again, and this change was even bigger. On June 1, 1939, the Japanese fleet began using a code that the Allies came to call JN-25. The Japanese—who had moved to using numbers rather than characters—now employed a massive codebook containing about 30,000 five-digit groups. They also had a new way of enciphering. Before the code was sent, each code group was enciphered by using math to apply an “additive.”
Here is how the additive method worked: When a Japanese cryptographer began encoding a single message, he would look in the codebook and find the five-digit group that stood for the word (or syllable or phrase or punctuation mark) he wanted. He would repeat that process until he got to the end of the message. Then he would get out a different book, called an additive book, turn to a page-selected at random, pick a five digit number, and add that to the first code group. He would add the next additive to the second. And so on. The Japanese code makers used a peculiar kind of math called noncarrying or “false” addition. There was no carrying of digits, so 8 plus 7 would equal 5, rather than 15. If the code group for “maru” was, say, 13563, and the additive was 24968, the resulting group would be 37421 (1 + 2 = 3; 3 + 4 = 7; 5 + 9 = 4; 6 + 6 = 2; 3 + 8 = 1). That was the group of digits that would be radioed. To crack a message, the Americans had to figure out the additive and subtract it to get the code group. Then they had to figure out what the code group stood for. Neither Driscoll nor anybody in the Navy operation had seen an additive cipher, but she figured it out. It took her less than a year to make a dent.
In December 1940, both code and cipher were changed to a system the Allies called JN-25B; the team stripped the additives and built a partial bank of code words. Then, in early December 1941—days before Pearl Harbor—the additive books were changed. The codebooks, at least, were not. The U.S. Navy was able to recover a certain amount of the new system—but not enough—before the attack on Pearl Harbor happened and all hell broke loose.
“If the Japanese Navy had changed the code-book along with the cipher keys on 1 December 1941, there is no telling how badly the war in the Pacific would have gone,” said Laurance Safford.
As crushing as Pearl Harbor was, it was thanks in large part to Driscoll’s decades-long detective work that America did not enter the second world war quite as blind as it might have seemed.
*Correction, Oct. 11, 2017: Due to a production error, this article originally used a photo depicting a different Agnes Meyer. The photo has been updated.
Excerpted from the book Code Girls: The Untold Story of the American Women Code Breakers of World War II by Liza Mundy, published on Oct. 10, 2017, by Hachette Books, a division of Hachette Book Group. Copyright 2017 Liza Mundy.
Future Tense is a collaboration among Arizona State University, New America, and Slate. Future Tense explores the ways emerging technologies affect society, policy, and culture. To read more, follow us on Twitter and sign up for our weekly newsletter.