On 10 May 2010, the Acquisitions Chairman (AC) Dave D’Auria met with Mrs. Cheryl Needle in Pepperell, MA to transfer the archive of Chaocipher material from the estate of inventor John Byrne to the National Cryptologic Museum. Chaocipher is the name Byrne (February 1880-April 1960) gave to a cipher system he invented in 1918.
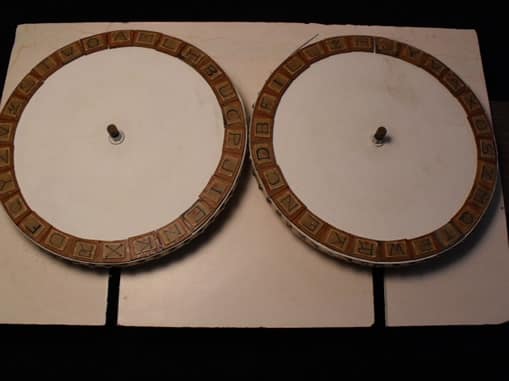
The AC negotiated the donation with Mrs. Needle who was acting on behalf of John Byrne’s daughter-in-law, Mrs. Patricia Byrne. The archive consisted of two boxes of notes, papers and personal correspondence from both the inventor John Byrne, and his son, John Byrne Jr.; two copies of John Byrne’s book The Silent Years; five Chaocipher blueprint drawings from 1920; and a large crude wooden mockup of the cipher wheel function of the original Chaocipher machine. The original cigar-box size Chaocipher machine was apparently destroyed, and only the blueprint drawings and the crude mock-up remain.
From the time of his invention in 1918 until his death in 1960, John Byrne tried to interest the U.S. government and various other organizations in his Chaocipher machine which he billed as absolutely unbreakable. Unfortunately neither he nor his invention were taken seriously by any U.S. government or commercial organization. This appears to be due in large part to Byrne’s refusal to provide those he approached with detailed technical information on Chaocipher, and the standard number and type of challenge messages requested from every cipher inventor that approached U.S. government, military and commercial organizations.
The archive of donated material includes four decades of correspondence between Byrne and, inter alia, the White House, the State Department, the War Department, the Attorney General’s Office, the Department of Justice, and the Navy Bureau of Engineering. Personal appeals during this period include letters to President and Mrs. Franklin Roosevelt, General Douglas MacArthur, and a host of other high-ranking U.S. government officials. Attempts to patent Chaocipher were rejected by at least two different patent attorney law firms, and attempts to “sell and tell” the Chaocipher story were rejected by Collier’s Weekly and the Saturday Evening Post. There were also “rejection” letters from Bell Laboratories and the Teletype corporation. Of particular interest are numerous exchanges between Byrne and both William Friedman and Colonel Parker Hitt, two of American’s leading cryptologists during this period. Colonel Hitt, the author and publisher of the first ever book on Cryptography by the US Army in 1916, The Manual for Solution of Military Ciphers, believed Byrne’s invention had merit but he also indicated that Chaocipher had critical shortfalls. Friedman’s exchanges with Byrne beginning in 1922 were official rejections of Chaocipher for use by the U.S. government, but at least one of them pointed Byrne towards the commercial market. One particularly testy exchange that occurred in 1954 was spurred by caustic remarks Friedman made about Byrne and Chaocipher at a 13 March presentation to the American Association of the University of Women. In a February 1957 letter responding to Friedman’s remarks, Byrne maintained his conviction that Chaocipher is “forever indecipherable”, and he issued a personal challenge to Friedman to “prove me wrong right away” by solving an enciphered excerpt from a speech made by General Douglas MacArthur. In a following 1957 letter Friedman declined the challenge.
In 1953 Byrne published his autobiography The Silent Years. Although the book was intended to be about his life-long friendship with James Joyce, inexplicably Byrne used Chapter 21 of the book to discuss his four-decade quest to convince people about the merits of Chaocipher. Chapter 21 contains examples of plaintext and corresponding ciphertext from Chaocipher, and a few enciphered lines whose plaintext is not provided.
Byrne challenged the world-at-large to decipher those few lines with a $5,000 prize for the first person able to do so. No one ever came forward to claim the prize. After John Byrne’s death in 1960, his son John Byrne Jr. continued with his father’s cause and tried in vain to market Chaocipher as either a machine or cryptologic algorithm. John Byrne Jr. has also sadly passed away without ever seeing any commercial success from his father’s invention. Chaocipher is on an infamous list of unsolved codes and ciphers and was a reference subject in David Kahn’s book, The Codebreakers. To date Chaocipher has not been cracked and it remains both a cryptologic curiosity and legend, and one of the premier unsolved cipher challenges of today.
For more information on legendary unsolved ciphers go to http://elonka.com/UnsolvedCodes.html. For more general information on Chaocipher and efforts to solve this enigma go to http://www.mountainvistasoft.com/chaocipher/
In June 2010 the NCMF/NCM shared some of the archive material with the amateur cipher public and within weeks the first-ever Chaocipher solution was published on the Internet. You can read more about Chaocipher and the solution to this system at http://www.mountainvistasoft.com/chaocipher/ActualChaocipher/Chaocipher-Revealed-Algorithm.pdf